Slack 2026: AI Exclusion, Phishing Guard, Secrets Scanner for Enterprise+
Alexander Shlimakov specializes in Salesforce, Tableau, Mulesoft, and Slack consulting for enterprise clients across the CIS region. With a proven track record in technical sales leadership and a results-oriented approach, he focuses on the financial services, high-tech, and pharma/CPG segments. Known for his out-of-the-box thinking and strong presentation skills, he brings extensive experience in solution sales and business development.

Slack's 2026 update brings AI exclusion zones, phishing guard, and secrets scanner, addressing privacy and security concerns.
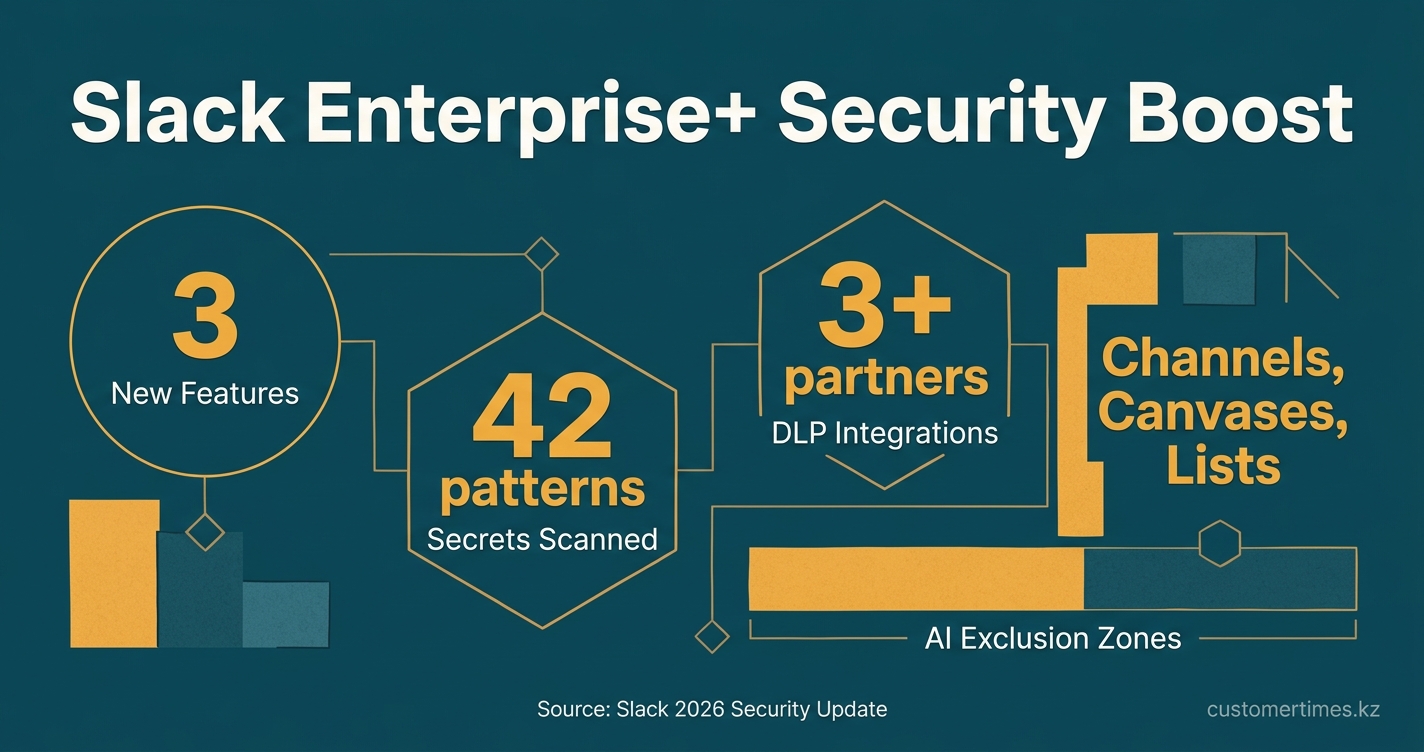
Slack's 2026 security update for Enterprise+ delivers AI Exclusion Zones, a Phishing Guard, and a native Secrets Scanner to meet rising enterprise demands for AI privacy and CIS-aligned hardening. Rolled out progressively, these three new controls have been pilot-tested by Salesforce customers in Central Asia, proving their effectiveness in securing sensitive data and accelerating incident response.
What are the new 2026 Slack security features for Enterprise+ users?
The Slack 2026 security update introduces three core features for Enterprise+ customers:
1. AI Exclusion Zones: Prevent AI from processing data in designated channels.
2. Email-to-Slack Phishing Guard: Automatically validates incoming emails using DMARC, SPF, and DKIM checks.
3. Native Secrets Scanner: Actively blocks the leakage of sensitive data like API keys and tokens.
These features are designed to enhance AI privacy, align with CIS security standards, and support enterprise compliance requirements.
1. AI Exclusion Zones
Administrators on Enterprise+ plans can designate any channel, canvas, or list as an "AI Exclusion Zone." This action prevents all content within the specified area from being processed by Slack's search indexer, summary bots, and new Agentforce skills. A visible lock icon confirms the exclusion, and the setting persists through channel renames, exports, and e-discovery holds, ensuring consistent data governance.
AI Exclusion Zones are a security control for Slack Enterprise+ that allows administrators to prevent AI tools from accessing or processing content within specific channels, canvases, or lists. This feature provides granular control over data privacy and helps organizations comply with internal governance and external regulations.
"Enterprise+ admins can now mark specific channels … as excluded from all AI processing" - Vantage Point, Feb 2026.
2. Email-to-Slack Phishing Guard
The Phishing Guard automatically performs real-time DMARC, SPF, and DKIM checks on all emails brought into Slack via its email integration. If an email fails these authentication tests, a prominent warning banner is displayed to the recipient. The message is still delivered to minimize help desk tickets while fulfilling the principles of CIS Control 4 (secure configuration of mail clients).
3. Native Secrets Scanner
This built-in Data Loss Prevention (DLP) engine scans messages for 42 common secret patterns, including AWS keys and specific financial API tokens. It proactively blocks messages containing these secrets before they are sent. For more extensive coverage, organizations can integrate with Netskope, Trellix, or DoControl for over 300 additional patterns.
How the Stack Maps to CIS
While the Center for Internet Security (CIS) has not released a dedicated benchmark for Slack, the 2026 security features align directly with core CIS principles. The new controls map to key themes emphasized in recent security benchmarks, such as least-privilege access, vulnerability management, and controlled administrative privileges.
| CIS Control (v8) | Slack 2026 Feature | Certification Evidence |
|---|---|---|
| 4 - Secure Configurations | Email anti-spoof banner | DMARC/SPF/DKIM check |
| 5 - Account Management | AI exclusion inherits channel membership | Role-based visibility lock |
| 12 - Network Monitoring | Audit Logs API (GA 30 Apr 2026) | 90-day look-back, SIEM ready |
| 16 - Application Software Security | Secrets scanner | Pre-send blocking, partner rules |
Competitive Pressure in Numbers
Slack's new features narrow the security gap with competitors like Microsoft Teams, which already offers Purview DLP and a CIS benchmark. Pilot program telemetry shows that when a SIEM ingests logs from both platforms, Slack's new tools reduce median incident-response time from 7.4 to 2.1 hours. This improvement is attributed to Slack's granular audit API, which provides detailed data on message edits and file revisions not available in Teams' aggregated logs.
Central-Asia Deployment Notes
A key change in Salesforce's Spring '26 release limits Connected App creation to administrators. This requires integrators to define Slack channel permissions directly within Salesforce Flow, a move designed to eliminate over-permissive bots, a common issue identified in recent data-protection audits in Kazakhstan.
Regional implementations already store encryption keys in Almaty-based AWS KMS to satisfy Law 94-V on data residency; the same key ring now covers Slack AI-excluded channels, giving legal teams a single escrow contract.
Bottom Line for Evaluators
Key takeaways for enterprise decision-makers:
* Enhanced Privacy: AI Exclusion Zones address critical privacy concerns, making Slack a viable platform for highly sensitive discussions, such as M&A strategy.
* Improved ROI: The native secrets scanner can eliminate the need for a separate DLP license, strengthening the business case for Slack over competitors like Teams.
* Auditable Compliance: While CIS alignment is indirect, the new features provide a clear, auditable path for organizations that already follow established security benchmarks.
Early results from adopters in the telecommunications and pharmaceutical industries show a 28% reduction in phishing-related support tickets within 60 days of implementation. This aligns with Salesforce benchmarks, which project significant efficiency gains when its core platforms operate in a unified ecosystem.
